Combining Cybersecurity Frameworks - An Alternative to Incident Reporting
Combining Cybersecurity Frameworks - An Alternative to Incident Reporting
Nota importada desde Inbox durante consolidacion bulk.
Overview
Reporting and sharing incident findings play a pivotal role in the cybersecurity community. Through this practice, organizations and security teams can derive valuable intelligence from past incidents, contributing to collective knowledge and strengthening defenses. When we speak of “benefiting,” it entails extracting insights into the Tactics, Techniques, and Procedures (TTPs) employed by threat actors who may target their organizations. This involves analyzing motives and the modus operandi, formulating effective detection rules, enriching intelligence datasets with Indicators of Compromise (IoCs), and implementing pertinent mitigation and hardening configurations. This article explores an alternative approach to incident reporting, aiming to uncover additional insights. The proposed alternative integrates three cybersecurity frameworks: the Cyber Kill Chain (CKC), Diamond Model (DM), and ATT&CK, offering a comprehensive perspective for enhanced threat intelligence consumption.
Background
Initially, let’s delve into the foundational background of the three frameworks that will be employed:
Cyber Kill Chain

Cyber Kill Chain Framework
The Cyber Kill Chain is a strategic framework developed by Lockheed Martin that outlines the stages of a cyber attack, providing a systematic approach for understanding and mitigating cyber threats. The framework consists of seven distinct phases:
- Reconnaissance: In this initial phase, adversaries gather information about the target, identifying potential vulnerabilities and gathering intelligence on the target’s systems and network architecture.
- Weaponization: In this phase, attackers develop or acquire malicious tools and create a payload to exploit the identified vulnerabilities.
- Delivery: Attackers deliver the weaponized payload to the target environment. This could be through methods such as email attachments, infected websites, or other means to deliver the malicious content to the victim’s system.
- Exploitation: Once the weaponized content reaches the target system, the attackers exploit vulnerabilities to gain unauthorized access. This phase involves executing the payload, taking advantage of weaknesses in the target’s security.
- Installation: After successful exploitation, the attacker installs malware or establishes a persistent presence on the compromised system.
- Command and Control (C2): Attackers establish communication channels between the compromised system and their infrastructure, enabling remote control.
- Actions on Objectives: In the final phase, attackers achieve their ultimate goals, which may include data exfiltration, system manipulation, or other malicious activities aligned with their objectives. This phase completes the cyber kill chain.
The Cyber Kill Chain framework is instrumental in guiding organizations to understand and disrupt the different stages of a cyber attack, emphasizing the importance of breaking the chain at any phase to prevent successful intrusions.
Diamond Model
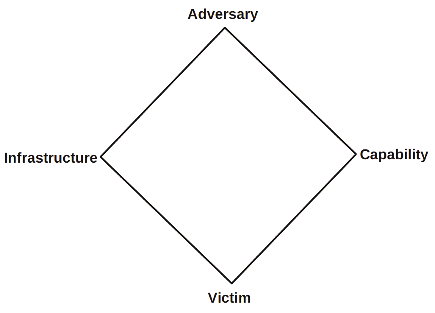
Diamond Model Framework
The Diamond Model is a conceptual framework designed for the analysis and visualization of cyber threat intelligence and incidents. Its basic features include four key elements arranged in a diamond-shaped configuration: Adversary, Infrastructure, Victim, and Capability. Each vertex of the diamond represents one of these elements, and the relationships and interactions among them provide a structured way to understand cyber threats.
- The Adversary vertex focuses on the threat actor or group responsible for the incident.
- The Infrastructure vertex considers the systems used in the attack.
- The Victim vertex represents the entity or entities targeted.
- The Capability vertex addresses the specific techniques or methods employed by the adversary.
The model’s also consists of meta-features, though not detailed here, add additional layers of analysis to enrich the understanding of cyber threats and aid in strategic decision-making. These meta-features are: Timestamp, Phase, Result, Direction, Methodology, Resources, Social-political, Technology.
ATT&CK

MITRE ATT&CK Framework
The MITRE ATT&CK framework is a comprehensive knowledge base that outlines the TTPs employed by cyber adversaries during different stages of the cyber attack lifecycle. The framework is structured hierarchically, with tactics representing high-level objectives and techniques representing specific methods to achieve those objectives.
- Tactics are categorized into domains such as Initial Access, Execution, Persistence, Privilege Escalation, Defense Evasion, Credential Access, Discovery, Lateral Movement, Collection, Exfiltration, Impact, and more.
- Each tactic is then associated with a variety of Techniques, which are the specific means adversaries use to execute the tactics. For instance, in the Execution tactic, a technique might be “ Command and Scripting Interpreter” (T1059), representing the use of command-line interfaces by attackers for code execution.
- Procedures, the lowest level of the framework, provide real-world examples of adversaries implementing specific techniques.
The ATT&CK framework serves as a valuable resource for understanding and improving defenses against a wide range of cyber threats.
Combining the Frameworks
We all have seen incident reports containing information based on these insightful frameworks, but we haven’t seen them combining them. Let’s establish a theory for linking them, and discuss if this approach provides additional value with an application example.
An example proposal for the combination is the following (this is just an example, someone can modify this with a different thinking):

CKC-DM-ATT&CK Linking Proposal
This example theory, maps the similar ATT&CK Tactics to their similar CKC phases (i.e. Command & Control is the same ). The rest of the ATT&CK Tactics are linked to the “Actions on Objectives” phase of the CKC, as someone can argue that these Tactics are utilized from the threat actors to achieve their objectives. On each CKC to ATT&CK combination, there is also the DM, from which there are utilized only the vertexes that apply. In example, in most scenarios, there are no enough artifacts to fill the Adversary vertex, thus it remains unfilled.
Application Example
Background
Now let’s apply our theory to a real incident reporting to explore this approach. We will utilize one (of the many) great report from The DFIR Report. More specifically, we will rely on the latest “Buzzing on Christmas Eve: Trigona Ransomware in 3 Hours” article.
This report discusses an incident where the threat actors exploited a publicly exposed Remote Desktop Protocol (RDP) host, leading to data exfiltration and the deployment of Trigona ransomware. Take some time to read it if its new for you, so you can have an understanding before delving deep in this application example.
Since we are now familiar with the technical findings, let’s try to apply our approach.
_Disclaimers_
- Not every mapping would be correct, the important part here is to explore the different approach.
- There is nothing wrong with the initial reporting structure of the DFIR Report. Οn the contrary, it is excellent and includes simple and insightful information. We just try to apply our theory on a real world incident report.
Applying the Approach
We will now start presenting the technical results of this incident using our described theory.
- We start with the Reconnaissance & Weaponization phases of the CKC. It is important to notice that due to lack of evidence and the difficulty in detecting such actions in these phases, the authors did not include specific information. However, based on the mentioned context, we tried to include those (for the purposes of applying the theory):
- For the Reconnaissance, we assumed that the threat actor manually searched the target through network tools i.e. Shodan or Censys, identified an exposed RDP service of a public facing IP of the organization they wanted to target, and gathered the Admin credentials for it i.e. from DarkWeb forums or leak sites.
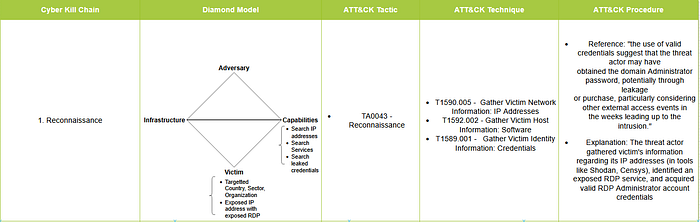
Reconnaissance phase
- For the Weaponization, we assumed that the threat actors may be bought this access from an Initial Access Broker (IAB) and developed their own tools (i.e. many custom BAT files).
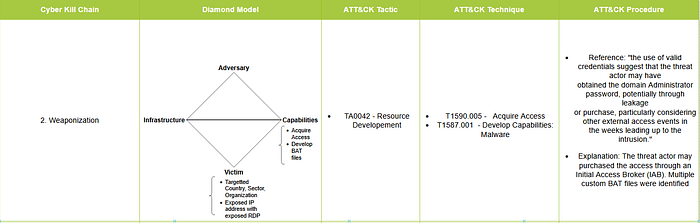
Weaponization phase
- For the Delivery, the threat actor used valid accounts to log in the external RDP service. This finding also included the source IPs and workstation names (which were also included in the Adversary and Infrastructure vertexes of the Diamond Model).
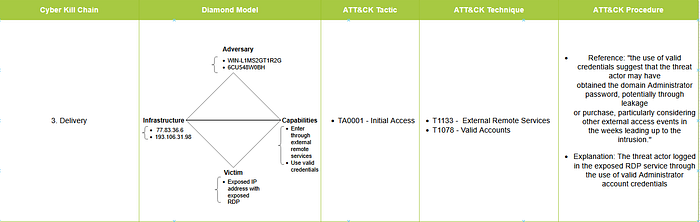
Delivery phase
- For the Exploitation, the threat actor utilized multiple BAT files that included CMD, PowerShell and Windows Management Instrumentation commands.
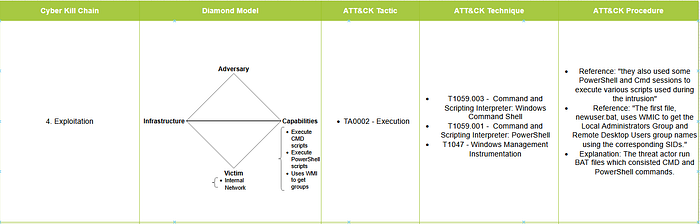
Exploitation phase
4. For the Installation, the threat actor created accounts, added them in privileged groups, and the final Trigona ransomware payload added a registry value in the Run registry key.
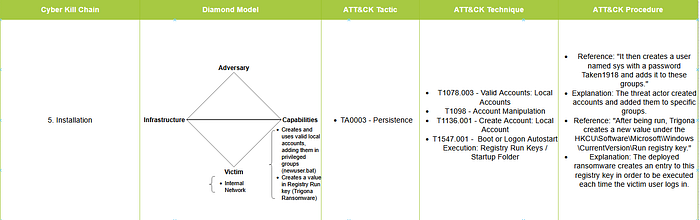
Installation phase
- For the Command and Control, the threat actor utilized remote access software (RDP) and dropped multiple BAT scripts.
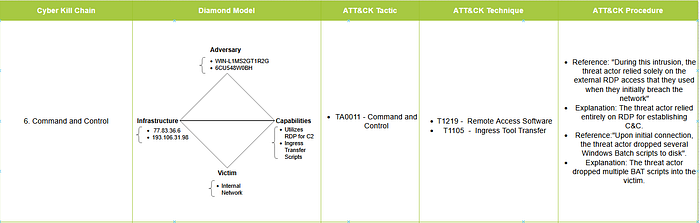
Command and Control phase
- Lastly, we end this application example with the Actions on Objectives phase, where a lot of combinations are depicted:
- For the Privilege Escalation, the threat actor utilized valid accounts with admin privileges.

Actions on Objectives phase — Privilege Escalation tactic
- For the Defense Evasion, the threat actor modified the registry (for hiding user accounts from the login) and disabling Windows Defender services using BAT files.
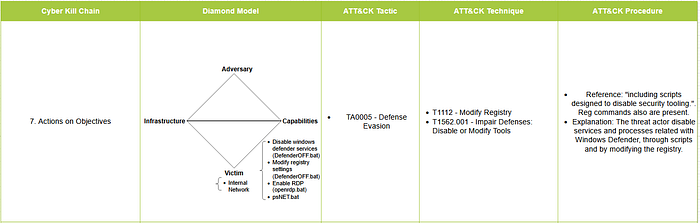
Actions on Objectives phase — Defense Evasion tactic
- For the Discovery, the threat actor utilized multiple tools and commands such as, ipinfo.bat, netscan.exe, sd.exe, whoami.exe, etc.
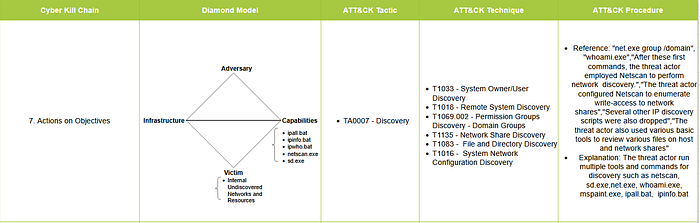
Actions on Objectives phase — Discovery tactic
- For the Lateral Movement, the threat actor utilized mostly RDP, along with SMB/Admin Shares (due to netscan’s psexec module), and laterally transferred each of their tools (BAT scripts, etc.).
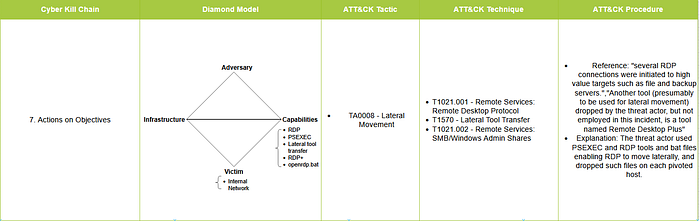
Actions on Objectives phase — Lateral Movement tactic
- For the Exfiltration, the threat actor utilized rclone.exe (symmetric encryption for its configuration) to exfiltrate the stolen data to a Mega.io account (cloud storage). Unfortunately, the Mega.io account was not identified. It would be a nice addition to the Infrastructure (Exfiltration URL) and the Adversary (threat actor’s account) vertexes.
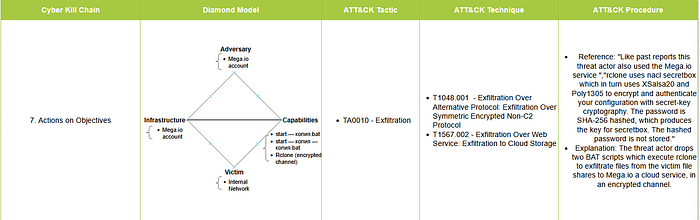
Actions on Objectives phase — Exfiltration tactic
- Lastly, for the Impact, the threat actor deployed Trigona ransomware, which encrypted the hosts’ data.
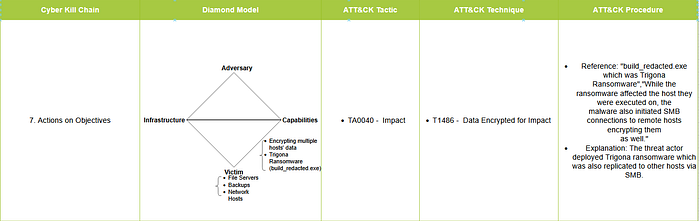
Actions on Objectives phase — Impact tactic
Conclusion
Sharing incident reporting findings is essential for the collective defense of the community, enabling proactive actions and preparation against evolving threats. The reporting methodology employed should yield valuable insights, spanning both technical details and high-level strategic considerations. In this article, we examined an innovative approach that combines the Cyber Kill Chain (CKC) phases, Diamond Model (DM) vertices, and MITRE ATT&CK tactics and techniques simultaneously. This holistic approach aims to capture both the technical intricacies and the modus operandi of threat actors. Your thoughts on this approach are highly welcomed. Feel free to share your feedback in the comment section on Medium or by commenting directly on my posts.
References
- https://attack.mitre.org/
- https://attack.mitre.org/docs/ATTACK_Design_and_Philosophy_March_2020.pdf
- https://warnerchad.medium.com/diamond-model-for-cti-5aba5ba5585
- https://www.activeresponse.org/wp-content/uploads/2013/07/diamond.pdf
- https://www.lockheedmartin.com/en-us/capabilities/cyber/cyber-kill-chain.html
- https://www.lockheedmartin.com/content/dam/lockheed-martin/rms/documents/cyber/LM-White-Paper-Intel-Driven-Defense.pdf
- https://thedfirreport.com/2024/01/29/buzzing-on-christmas-eve-trigona-ransomware-in-3-hours/